| Version 1 (modified by , 3 years ago) ( diff ) |
|---|
Shibboleth SPv3 Installation on Ubuntu 22.04 LTS
Installation assumes you have already installed Ubuntu Server 22.04 with default configuration and has a public IP connectivity with DNS setup
Install Apache and Web applications
Once logged in you need to update the Ubuntu package repository.
sudo apt update
Then install the web server.
sudo apt install apache2
Check the apache version
apache2 -v
Now visit your server through the IP address. http://server_ip_address.
PHP Installation
Then install PHP and related modules for apache server and MariaDB.
sudo apt install php libapache2-mod-php php-mysql
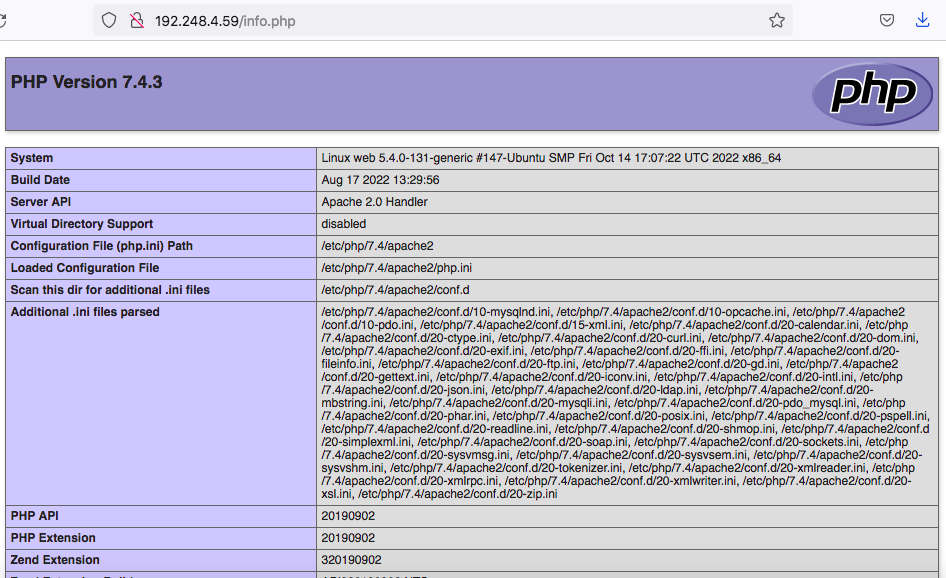
To test that your system is properly configured for PHP, create a PHP script called info.php. Here we will create at the root directory.
sudo nano /var/www/html/info.php
Insert the following command to show the php information.
<?php phpinfo(); ?>
Next go to http://your_IP/info.php URL and you will get page showing the php information,
MariaDB DBMS Installation
Here we will choose MariaDB DBMS as our database application. Install this using below command.
sudo apt install mariadb-server mariadb-client
Once installed check the version,
mysql --version
For mysql there is a script that strengthen the mariaDB server security. It is a series of yes no questions which removes initial weaknesses of the server.
To execute the scripts,
sudo mysql_secure_installation
NOTE: RUNNING ALL PARTS OF THIS SCRIPT IS RECOMMENDED FOR ALL MariaDB
SERVERS IN PRODUCTION USE! PLEASE READ EACH STEP CAREFULLY!
In order to log into MariaDB to secure it, we'll need the current
password for the root user. If you've just installed MariaDB, and
haven't set the root password yet, you should just press enter here.
Enter current password for root (enter for none):
OK, successfully used password, moving on...
Setting the root password or using the unix_socket ensures that nobody
can log into the MariaDB root user without the proper authorisation.
You already have your root account protected, so you can safely answer 'n'.
Switch to unix_socket authentication [Y/n] n
... skipping.
You already have your root account protected, so you can safely answer 'n'.
Change the root password? [Y/n] y
New password:
Re-enter new password:
Password updated successfully!
Reloading privilege tables..
... Success!
By default, a MariaDB installation has an anonymous user, allowing anyone
to log into MariaDB without having to have a user account created for
them. This is intended only for testing, and to make the installation
go a bit smoother. You should remove them before moving into a
production environment.
Remove anonymous users? [Y/n] y
... Success!
Normally, root should only be allowed to connect from 'localhost'. This
ensures that someone cannot guess at the root password from the network.
Disallow root login remotely? [Y/n] y
... Success!
By default, MariaDB comes with a database named 'test' that anyone can
access. This is also intended only for testing, and should be removed
before moving into a production environment.
Remove test database and access to it? [Y/n] y
- Dropping test database...
... Success!
- Removing privileges on test database...
... Success!
Reloading the privilege tables will ensure that all changes made so far
will take effect immediately.
Reload privilege tables now? [Y/n] y
... Success!
Cleaning up...
All done! If you've completed all of the above steps, your MariaDB
installation should now be secure.
Thanks for using MariaDB!
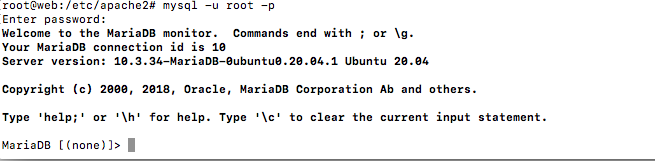
To login MariaDB enter below command and use the password entered above.
mysql -u root -p
To exit type,
exit
Apache Virtual Host Configuration
First we are going to install Moodle LMS and enable Shibboleth login for that. now let's make a directory for hosting Moodle web site.
sudo mkdir -p /var/www/lms.your_domain.com/public_html
We are going to host a moodle site too. Add a configuration file as below.
sudo nano /etc/apache2/sites-available/lms.your_domain.com.conf
<VirtualHost *:80>
ServerName lms.your_domain.com
ServerAlias lms.your_domain.com
ServerAdmin webmaster@lms.your_domain.com
DocumentRoot /var/www/lms.your_domain.com/public_html
<Directory /var/www/lms.your_domain.com/public_html>
Options -Indexes +FollowSymLinks
</Directory>
ErrorLog ${APACHE_LOG_DIR}/lms.your_domain.com-error.log
CustomLog ${APACHE_LOG_DIR}/lms.your_domain.com-access.log combined
</VirtualHost>
Once we do the configurations we have to enable the created sites as below,
sudo a2ensite lms.your_domain.com
Once done, test the configuration for any syntax errors with.
sudo apachectl configtest
Restart the Apache service for the changes to take effect.
sudo systemctl restart apache2
Now we are done with configurations of apache virtual hosting.
Here we have to create SSL certificates and assign them to the virtual hosts created. We can create SSL certificates using three methods.
- Generate a self-signed certificates (Steps 5 to 9)
- Create certificates using Let's Encrypt free SSL service. (Steps 10 to )
- Receiving certificates from a Commercial Certificate Authority.
As below you can use any of the above methods. Follow the steps as you prefer.
- Let'sencrypt setup (Skip this step if you already configured SSL with self signed or CA provided certificates)
Install Letsencypt and enable https
apt install certbot python3-certbot-apache certbot --apache
Go through the interactive prompt and include your server details. Make sure you select redirect option when asked.
Let's forward http traffic to https
RewriteEngine on RewriteCond %{SERVER_NAME} =lms.YOUR-DOMAIN RewriteRule https://%{SERVER_NAME}%{REQUEST_URI} [END,NE,R=permanent] # port 80 -- > 443 redirection
Then enable the Apache rewrite module.
sudo a2enmod rewrite
Install Shibboleth Service Provider
- Install Shibboleth SP:
apt install libapache2-mod-shib ntp --no-install-recommends
From this point the location of the SP directory is: /etc/shibboleth
Configure Shibboleth SP
- Download Federation Metadata Signing Certificate:
cd /etc/shibboleth/ wget https://fr.ac.lk/signedmetadata/metadata-signer -O federation-cert.pem
- Edit shibboleth2.xml opportunely:
nano /etc/shibboleth/shibboleth2.xml
...
<ApplicationDefaults entityID="https://sp.YOUR-DOMAIN/shibboleth"
REMOTE_USER="eppn subject-id pairwise-id persistent-id"
cipherSuites="DEFAULT:!EXP:!LOW:!aNULL:!eNULL:!DES:!IDEA:!SEED:!RC4:!3DES:!kRSA:!SSLv2:!SSLv3:!TLSv1:!TLSv1.1">
...
<Sessions lifetime="28800" timeout="3600" relayState="ss:mem" checkAddress="false" handlerSSL="true" cookieProps="https">
...
<SSO discoveryProtocol="SAMLDS" discoveryURL="https://fds.ac.lk">
SAML2
</SSO>
...
<MetadataProvider type="XML" url="https://fr.ac.lk/signedmetadata/metadata.xml" legacyOrgName="true" backingFilePath="test-metadata.xml" maxRefreshDelay="7200">
<MetadataFilter type="Signature" certificate="federation-cert.pem" verifyBackup="false"/>
<MetadataFilter type="RequireValidUntil" maxValidityInterval="864000" />
</MetadataProvider>
<!-- Simple file-based resolvers for separate signing/encryption keys. -->
<CredentialResolver type="File" use="signing"
key="sp-signing-key.pem" certificate="sp-signing-cert.pem"/>
<CredentialResolver type="File" use="encryption"
key="sp-encrypt-key.pem" certificate="sp-encrypt-cert.pem"/>
- Create SP metadata credentials:
/usr/sbin/shib-keygen -n sp-signing -e https://sp.YOUR-DOMAIN/shibboleth /usr/sbin/shib-keygen -n sp-encrypt -e https://sp.YOUR-DOMAIN/shibboleth shibd -t /etc/shibboleth/shibboleth2.xml (Check Shibboleth configuration)
- Enable Shibboleth Apache2 configuration:
a2enmod shib systemctl reload apache2.service
- Now you are able to reach your Shibboleth SP Metadata on:
https://sp.YOUR-DOMAIN/Shibboleth.sso/Metadata (change sp.YOUR-DOMAIN to you SP full qualified domain name)
- Register your SP on LEARN test federation:
Go to https://liaf.ac.lk/#join and follow the Service provider registration. Once the federation operator approves your request, you will be asked to use the content of your metadata file on federation registry registration.
You may have to answer several questions describing your service to the federation provider.
Configure Moodle as an Federated Resource
Here as a prerequisite you need a working moodle installation at the path https://sp.YOUR-DOMAIN/moodle. For this please refer to the link here.
- Create the Apache2 configuration for Moodle:
nano /etc/apache2/sites-available/moodle.conf
<Location /moodle>
#ShibRequestSetting applicationId mdl
</Location>
<Directory /var/www/html/moodle/auth/shibboleth/index.php>
AuthType shibboleth
#ShibRequestSetting applicationId mdl
ShibRequireSession On
require valid-user
</Directory>
- Then enable the site and restart the apache and shibboleth daemon to make changes to effect.
a2ensite mooodle systemctl restart shibd systemctl restart apache2
Now you may browse to https://sp.YOUR-DOMAIN/moodle and select your IDP to log in.
Attachments (1)
-
web31.png
(38.2 KB
) - added by 3 years ago.
web31
Download all attachments as: .zip