Secure SHell (SSL)
In this lab we are using your host machine as the ssh client and your Ubuntu VM as the ssh server. Download following applications
Setting up virtualbox
Installation of virtualbox and Downloading Ubuntu iso image
- Download and install virtualbox 5.0.x
- Download Ubuntu 18.04 Ubuntu image from the LEARN mirror
- Note down the location of downloaded iso file
Creating the VM
- Start virtualbox and Click on New button (at top-right) to create new virtual machine
- Enter name of the VM as: Ubuntu.
- Select OS Type: Linux
- Select Version: Ubuntu (64-bit)
- Then click on Continue button
- Set VM's memory size to 1024MB and click on Continue button
- Set VM's hard disk option to Create a virtual hard disk now and then click on Continue
- Select disk type to VDI
- Select storage type to Fixed size and Continue
- Make sure virtual hard disk file name in following format Ubuntu
- adjust the disk size to 12.0GB and click on Create to create the VM
This might take couple of minutes
(Note down the location of vdi image file when virtualbox flashes it on the screen)
Setting up Network Interface
- Select the VM from left panel on Virtual box, right click and open Settings
- Click on the Network title
- On Adapter 1 While Enable Network Adapter selected choose Attached to be Bride Adapter. This virtual interface will work as the WAN port of the firewall (Can be connect from out side).
Setting up boot device and Booting
- Click on Storage title and select CD ROM icon with Caption "Empty" under the Controller:IDE, Click on CD ROM icon under the Attribute on the left side to select
- Choose Virtual Optical Disk File
- Locate the Ubuntu CD Image file you downloaded from the LEARN ftp. Press OK to close the settings window.
- Right click on VM and select Start to make a Normal Start. You should now see a separate window with Installation screen"
Installation
Installation is quite simple. You can figure it out your self (Next... Next... Next)
Setting UP IP Addresses
After you install the Ubuntu OS change the IP address. You can find your IP address from here
Run the commands below to create a new network configuration file
sudo vi /etc/netplan/50-cloud-init.yaml
Press i to edit the file
Then configure IPv4 addresses as shown below
# This file describes the network interfaces available on your system
# For more information, see netplan(5).
network:
version: 2
renderer: networkd
ethernets:
ens33:
dhcp4: no
dhcp6: no
addresses: [<Your IP address>/<Subnet>]
gateway4: 192.248.6.254
nameservers:
addresses: [192.248.1.161]
Exit and save your changes by pressing esc and type :wq
Run the commands below.
sudo netplan apply
Check the connectivity
Password Based Authentication
- Go to your host machine.
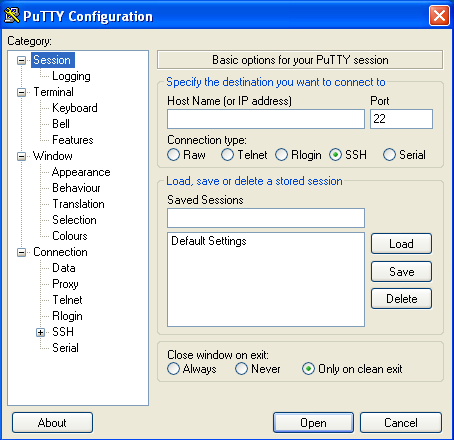
- Start PuTTY utility, by double-clicking on its .exe file.
- In the Host Name field, enter the IP address/Hostname of ssh server
- Click open.
- It will ask for username followd by password.
- Logout/close this session.
Public Key Authentication
Generating OpenSSH-compatible Keys for Use with PuTTY
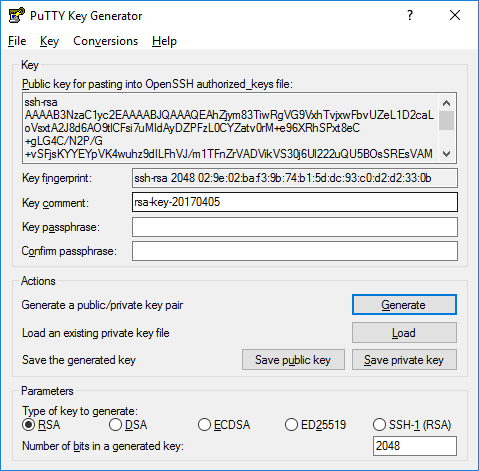
To generate a set of RSA keys with PuTTYgen
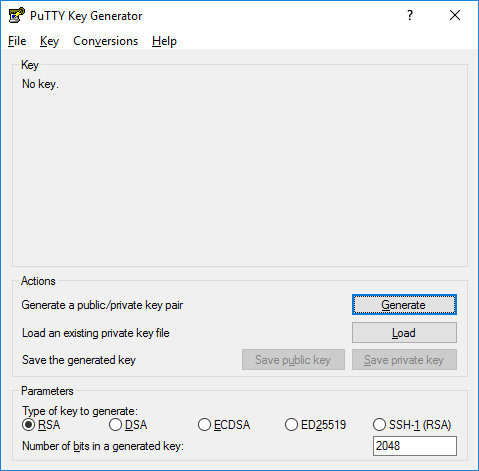
- Start the PuTTYgen utility, by double-clicking on its .exe file.
- For Type of key to generate, select SSH-2 RSA
- In the Number of bits in a generated key field, specify either 2048 or 4096 (increasing the bits makes it harder to crack the key by brute-force methods).
- Click the Generate button.
- Move your mouse pointer around in the blank area of the Key section, below the progress bar (to generate some randomness) until the progress bar is full.
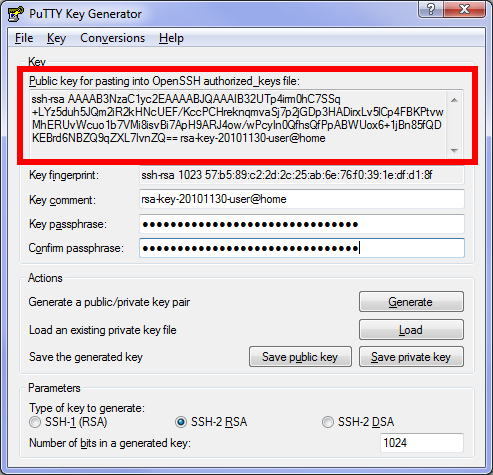
- A private/ public key pair has now been generated.
- In the Key comment field, enter your email address.
- The Key passphrase field & re-type the same passphrase in the Confirm passphrase field.9. Click the Save private key button and save as private_key .
- Right-click in the text field labeled Public key for pasting into OpenSSH authorized_keys file and choose Select All.
- Right-click again in the same text field and choose Copy.
- Open notepad; paste the public key and save it as txt file.
Save The Public Key On The Server
Now, you need to paste the copied public key in the file ~/.ssh/authorized_keys on your server.
- Log in to your destination server using putty with username apnic
- If your SSH folder does not yet exist, create it manually
mkdir ~/.ssh chmod 0700 ~/.ssh touch ~/.ssh/authorized_keys chmod 0644 ~/.ssh/authorized_keys
- Paste the SSH public key into your ~/.ssh/authorized_keys file:
sudo vi ~/.ssh/authorized_keys
- Tap the i key on your keyboard & right-click your mouse to paste.
- To save, tap the following keys on your keyboard (in this order): Esc, :wq Enter.
Create a PuTTY Profile to Save Your Server’s Settings
In PuTTY, you can create (and save) profiles for connections to your various SSH servers, so you don't have to remember, and continually re-type, redundant information.
- Start PuTTY by double-clicking its executable file.
- PuTTY's initial window is the Session Category (navigate PuTTY's various categories, along the left- hand side of the window).
- In the Host Name field, enter the IP address/Hostname of ssh server
- Enter the port number in the Port field as 22
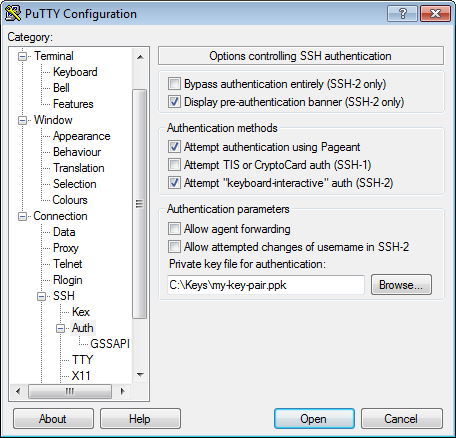
- Along the left-hand side of the window, select Connection > SSH > Auth
- Browse your file system and select your previously-created private key.
- Return to the Session Category and enter a name for this profile in the Saved Sessions field.
- Click the Save button for the Load, Save or Delete a stored session area.
Now you can go ahead and log in and you will not be prompted for a password. However, if you had set a passphrase on your public key, you will be asked to enter the passphrase at that time (and every time you log in, in the future).
Two Factor Authenticating
We will enable two factor authentication in out ubuntu server. To implement that we are going to use multifactor authentication with Google Authenticator.
Google auhtenticator
- Install Google Authenticator from following link in your Android device/iPhone/iPad/BlackBerry/Firefox devices
https://support.google.com/accounts/answer/1066447?hl=en
- Follow the instruction and install the app in your mobile.
- Or you can search for google-autheticator in Google Play or Apple Store.
Create an Authentication Key
- Go to the Ubuntu VM
- Install google-authenticator module first:
sudo apt-get update sudo apt-get install libpam-google-authenticator
- Log in as the user you’ll be logging in with remotely and run the google-authenticator command to create a secret key for that user.
$ google-authenticator Do you want authentication tokens to be time-based (y/n) y
- You will get some QR code ouput like bellow:
You will be prompted for some configurations.
- Scan the QRcode that appears with the Google Authenticator app or you can add the secret key Google Authenticator app.
- Save the backup codes listed somewhere safe. They will allow you to regain access if you lose your phone with the Authenticator app.
- Next it will ask several question; unless you have a good reason to, the defaults presented are sane. Just enter "y" for them.
Do you want me to update your "/home/fakrul/.google_authenticator" file (y/n) Do you want to disallow multiple uses of the same authentication token? This restricts you to one login about every 30s, but it increases your chances to notice or even prevent man-in-the-middle attacks (y/n) By default, tokens are good for 30 seconds and in order to compensate for possible time-skew between the client and the server, we allow an extra token before and after the current time. If you experience problems with poor time synchronization, you can increase the window from its default size of 1:30min to about 4min. Do you want to do so (y/n) If the computer that you are logging into isn't hardened against brute-force login attempts, you can enable rate-limiting for the authentication module. By default, this limits attackers to no more than 3 login attempts every 30s. Do you want to enable rate-limiting (y/n)
Enable two factor authentication for SSH
- Edit the /etc/pam.d/sshd file
sudo vi /etc/pam.d/sshd
- Add the following line:
auth required pam_google_authenticator.so
- :wq Save and quit.
- Edit /etc/ssh/sshd_config file
sudo vi /etc/ssh/sshd_config
- Search for ChallengeResponseAuthentication and replace no with yes
ChallengeResponseAuthentication yes
- :wq Save and quit.
- Now you need to reload the ssh service. You can do it to way:
sudo service ssh restart
Login to the server
Try to ssh to the server from a new terminal. It will ask for the verification code.
Attachments (6)
- putty.png (19.2 KB ) - added by 8 years ago.
- puttyauth.png (18.4 KB ) - added by 8 years ago.
- puttygen.png (24.5 KB ) - added by 8 years ago.
- puttygen1.png (12.9 KB ) - added by 8 years ago.
- puttygen2.png (45.1 KB ) - added by 8 years ago.
- qr.png (18.9 KB ) - added by 8 years ago.
Download all attachments as: .zip