What is a Firewall?
Firewall is a network security system that filters and controls the traffic on a predetermined set of rules. This is an intermediary system between the device and the internet.
How the Firewall of Linux works:
Most of the Linux distro’s ship with default firewall tools that can be used to configure them. We will be using “IPTables” the default tool provided in Linux to establish a firewall. Iptables is used to set up, maintain and inspect the tables of the IPv4 and IPv6 packet filter rules in the Linux Kernel.
iptables Lab
In this lab, you will setup a Basic Firewall Rules with iptables. Download Ubuntu_GUI VM from following link.
https://docs.learn.ac.lk/index.php/s/4Dpp3HUTbR8TaQk
User Name:user
Password:1234
Chains :-
Chains are a set of rules defined for a particular task.
We have three chains(set of rules) which are used to process the traffic:-
- INPUT Chains
- OUTPUT Chains
- FORWARD Chains
1. INPUT Chains
Any traffic coming from the internet(network) towards your local machine has to go through the input chains. That means they have to go through all the rules that have been set up in the Input chain.
2. OUTPUT Chains
Any traffic going from your local machine to the internet needs to go through the output chains.
3. FORWARD Chain
Any traffic which is coming from the external network and going to another network needs to go through the forward chain. It is used when two or more computers are connected and we want to send data between them.
Different Policies :-
There are three actions which the iptables can perform on the traffic
1.ACCEPT
2.DROP
3.REJECT
1. ACCEPT
When traffic passes the rules in its specified chain, then the iptable accepts the traffic. That means it opens up the gate and allows the person to go inside the kingdom.
2. DROP
When the traffic is unable to pass the rules in its specified chain, the iptable blocks that traffic. That means the firewall is closed.
3. REJECT
This type of action is similar to the drop action but it sends a message to the sender of the traffic stating that the data transfer has failed. As a general rule, use REJECT when you want the other end to know the port is unreachable’ use DROP for connections to hosts you don’t want people to see.
NOTE:-
You need to keep in mind a simple rule here:-
The Rules you set in the iptables are checked from the topmost rules to the bottom. Whenever a packet passes any of the top rules, it is allowed to pass the firewall. The lower rules are not checked. So be careful while setting up rules.
Basic iptables commands :
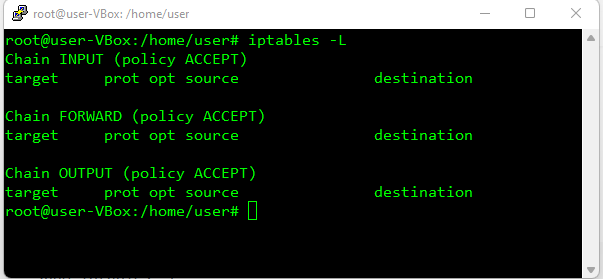
1.To list the rules of the current iptables:-
sudo iptables -L
The Output would be:-
As you can see, we have three chains (INPUT, FORWARD, OUTPUT). We can also see column headers, but they are no actual rules. This is because most of the Linux come with no predefined rules.
Let see what each column mean.
Target:-
This defines what action needs to be done on the packet (ACCEPT,DROP,etc..)
prot:-
This defines the protocol (TCP,IP) of the packet.
source:-
This tells the source address of the packet.
destination:-
This defines the destination address of the packet
2. Clear the rules : If you ever want to clear/flush out all the existing rules. Run the following command:-
sudo iptables -F
This will reset the iptables.
3. Changing the default policy of chains :
sudo iptables -P Chain_name Action_to_be_taken
Before making our firewall rules, check your connection to Ubuntu Machine using following methods. Please replace VM ip according to your setup. You can view your ip either using GUI or Terminal.
- Ping from your host machine to ubuntu VM
ping <ubuntu VM ip>
- Check web server by typing following in your Host machine browser
http://ubuntu VM ip
- Using a VNC client. (if you don't have vnc client in host pc, please install)
Making your First Rule :
1. Implementing a DROP rule :
We’ll now start building our firewall policies.We’ll first work on the input chain since that is where the incoming traffic will be sent through.
Syntax:-
sudo iptables -A/-I chain_name -s source_ip -j action_to_take
We’ll take an example to understand the topic.
Let’s assume we want to block the traffic coming from an IP address 192.168.1.4. The following command can be used:-
sudo iptables -A INPUT -s 192.168.1.4 -j DROP
This may look complicated, but most of it will make sense when we go over the components:-
-A INPUT :-
The flag -A is used to append a rule to the end of a chain. This part of the command tells the iptable that we want to add a rule to the end of the INPUT chain.
-I INPUT:- In this flag the rules are added to the top of the chain.
-s 192.168.1.4:- The flag -s is used to specify the source of the packet. This tells the iptable to look for the packets coming from the source 192.168.1.4
-j DROP This specifies what the iptable should do with the packet.
In short, the above command adds a rule to the INPUT chain which says, if any packet arrives whose source address is 192.168.1.4 then drop that packet, that means do not allow the packet reach the computer.
As a result it will disconnect your ssh connection to Ubuntu Machine.
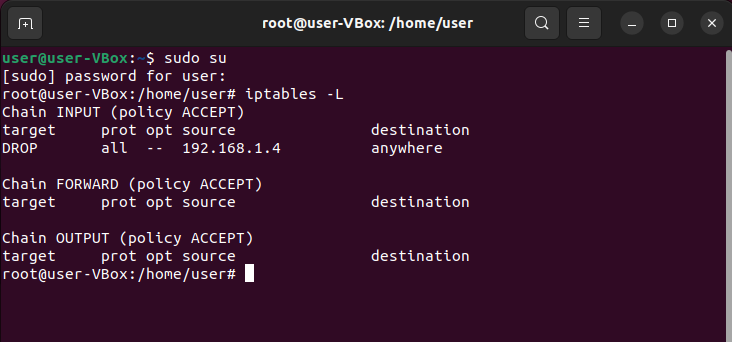
Now go to Ubuntu Desktop and open the Terminal program and execute following command as root.
Once you execute the above command you can see the changes by using the command:-
sudo iptables -L
The Output would be:-
2. Implementing a ACCEPT rule : If you want to add rules to specific ports of your network,then the following commands can be used.
Syntax:-
sudo iptables -A/-I chain_name -s source_ip -p protocol_name --dport port_number -j Action_to_take
-p protocol_name:- This option is used to match the packets that follow the protocol protocol_name.
-dport port_number: This is option is available only if you give the -p protocol_name option. It specifies to look for the packets that are going to the port “port_number”.
Example:-
Let’s say we want to keep our SSH port open (we will assume in this guide that the default SSH port is 22) from the 192.168.1.4 network we blocked in the above case. That is we only want to allow those packets coming from 192.168.1.4 and which wants to go to the port 22.
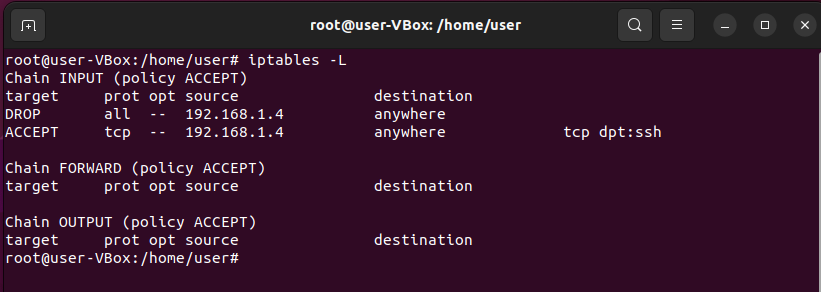
sudo iptables -A INPUT -s 192.168.1.4 -p tcp --dport 22 -j ACCEPT
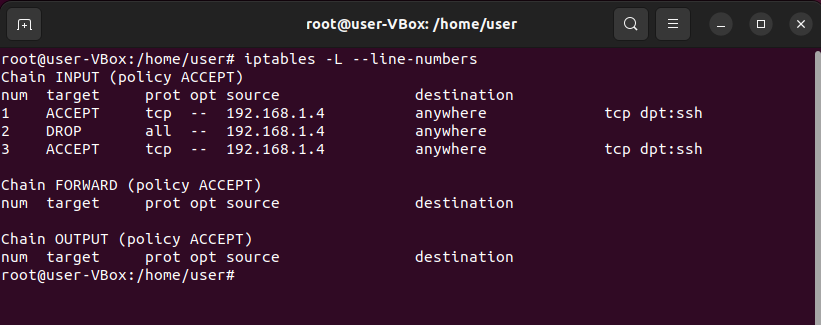
Now try to connect via SSH, Still cannot?, then check iptables;
sudo iptables -L
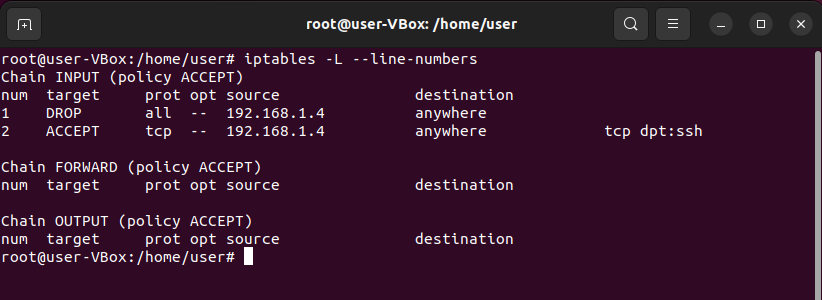
Can you guess the issue? hope you will.This is due to rules are executed from top to bottom. Enter following command to see the rules order(Numbers).
sudo iptables -L --line-numbers
You have 2 fixes to resolve this, Either add SSH Rule to Top Or Deleting DROP All rule. Replace -A with -I. Now check the IP tables.
3. Add a rule to TOP of the iptable :
sudo iptables -I INPUT -s 192.168.1.4 -p tcp --dport 22 -j ACCEPT
Now you will be able to SSH in to Ubuntu VM. Then we can delete the Duplicating rule.
4. Deleting a rule from the iptable :
Syntax:-
sudo iptables -D chain_name rule_number
Example:-
If we want to delete the rule which accepts the traffic to port 22 and which we have added in the previous section, then:-
sudo iptables -D INPUT 3
Remember the rules number starts from 1
5. Add a rule for subnet :
sudo iptables -A INPUT -s 192.168.1.0/24 -j DROP
6. Add a rule for specific position (Rule number):
Following command will add the rule to number 2 position.
sudo iptables -I INPUT 2 -s 192.168.1.0/24 -j DROP
7. Saving your configuration : Optional (Don't DO for this Lab)
This part is unnecessary if you are implementing it on a personal computer which is not a server, but if you are implementing a firewall on a server, then there are high chances that your server might get corrupted and you might lose all your data. So, it’s always better to save your configurations.
There are a lot of ways to do this, but the easiest way I find is with iptables-persistent package. You can download the package from Ubuntu’s default repositories:
sudo apt-get update sudo apt-get install iptables-persistent
Once the installation is complete, you can save your configuration using the command:-
sudo invoke-rc.d iptables-persistent save
Exercise
- Add a rule to access the web server of Ubuntu VM.(port 80)
- Add a rule to access the VNC server of Ubuntu VM.(port 5900)
- Drop all traffic form 192.168.1.0/24 (your local Network) and allow only SSH from your Host PC.
Flush IP Tables
Before we proceed with UFW lab. We will remove all iptables entries with following command.
iptables -F
UFW Lab
Introduction
UFW (uncomplicated firewall) is a firewall configuration tool that runs on top of iptables, included by default within Ubuntu distributions. It provides a streamlined interface for configuring common firewall use cases via the command line.
Verify UFW Status
To check if ufw is enabled, run:
sudo ufw status
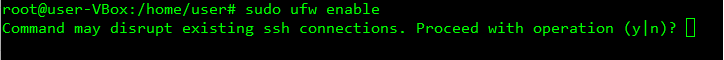
Enable UFW
If you got a Status: inactive message when running ufw status, it means the firewall is not yet enabled on the system. You’ll need to run a command to enable it.
sudo ufw enable
You’ll see output like this:
if you select Yes your SSH connection will May Drop. But as we have Terminal access we will proceed. Later in this Lab we will learn how to avoid this problem.
Output Firewall is active and enabled on system startup
check the status with -verbose parameter
sudo ufw status verbose
Disable UFW
If for some reason you need to disable UFW, you can do so with the following command
sudo ufw disable
Be aware that this command will fully disable the firewall service on your system.
Block an IP Address
To block all network connections that originate from a specific IP address, run the following command, replacing the highlighted IP address with the IP address that you want to block:
sudo ufw deny from 203.0.113.100
Output Rule added
In this example, from 203.0.113.100 specifies a source IP address of “203.0.113.100”.
If you run sudo ufw status now, you’ll see the specified IP address listed as denied:
Output Status: active To Action From -- ------ ---- Anywhere DENY 203.0.113.100
Block a Subnet
If you need to block a full subnet, you may use the subnet address as from parameter on the ufw deny command. This would block all IP addresses in the example subnet 203.0.113.0/24:
sudo ufw deny from 203.0.113.0/24
Output Rule added
Block Incoming Connections to a Network Interface
To block incoming connections from a specific IP address to a specific network interface, run the following command, replacing the highlighted IP address with the IP address you want to block:
sudo ufw deny in on eth0 from 203.0.113.100
The in parameter tells ufw to apply the rule only for incoming connections, and the on eth0 parameter specifies that the rule applies only for the eth0 interface. This might be useful if you have a system with several network interfaces (including virtual ones) and you need to block external access to some of these interfaces, but not all.
Allow an IP Address
To allow all network connections that originate from a specific IP address, run the following command, replacing the highlighted IP address with the IP address that you want to allow access:
sudo ufw allow from 203.0.113.101
If you run sudo ufw status now, you’ll see output similar to this, showing the word ALLOW next to the IP address you just added.
Output Status: active To Action From -- ------ ---- ... Anywhere ALLOW 203.0.113.101
You can also allow connections from a whole subnet by providing the corresponding subnet mask for a host, such as 203.0.113.0/24.
To insert a rule to specific position
sudo ufw insert 3 deny from 192.168.1.10
above command will add the rule at 3rd position.
sudo ufw status numbered
Delete UFW Rule
To delete a rule that you previously set up within UFW, use ufw delete followed by the rule (allow or deny) and the target specification. The following example would delete a rule previously set to allow all connections from an IP address of 203.0.113.101:
sudo ufw delete allow from 203.0.113.101
Another way to specify which rule you want to delete is by providing the rule ID. This information can be obtained with the following command:
sudo ufw status numbered
Output
Status: active
To Action From
-- ------ ----
[ 1] Anywhere DENY IN 203.0.113.100
[ 2] Anywhere on eth0 ALLOW IN 203.0.113.102
From the output, you can see that there are two active rules. The first rule, with highlighted values, denies all connections coming from the IP address 203.0.113.100. The second rule allows connections on the eth0 interface coming in from the IP address 203.0.113.102.
Because by default UFW already blocks all external access unless explicitly allowed, the first rule is redundant, so you can remove it. To delete a rule by its ID, run:
sudo ufw delete 1
You will be prompted to confirm the operation and to make sure the ID you’re providing refers to the correct rule you want to delete.
Output Deleting: deny from 203.0.113.100 Proceed with operation (y|n)? y Rule deleted
List Available Application Profiles
Upon installation, applications that rely on network communications will typically set up a UFW profile that you can use to allow connection from external addresses. This is often the same as running ufw allow from, with the advantage of providing a shortcut that abstracts the specific port numbers a service uses and provides a user-friendly nomenclature to referenced services.
To list which profiles are currently available, run the following;
sudo ufw app list
Enable Application Profile
To enable a UFW application profile, run ufw allow followed by the name of the application profile you want to enable, which you can obtain with a sudo ufw app list command. In the following example, we’re enabling the OpenSSH profile, which will allow all incoming SSH connections on the default SSH port.
sudo ufw allow “OpenSSH”
Output Rule added Rule added (v6)
Remember to quote profile names that consist of multiple words, such as Nginx HTTPS.
Disable Application Profile
To disable an application profile that you had previously set up within UFW, you’ll need to remove its corresponding rule. For example, consider the following output from sudo ufw status:
sudo ufw status
Output Status: active To Action From -- ------ ---- OpenSSH ALLOW Anywhere Nginx Full ALLOW Anywhere OpenSSH (v6) ALLOW Anywhere (v6) Nginx Full (v6) ALLOW Anywhere (v6)
This output indicates that the Nginx Full application profile is currently enabled, allowing any and all connections to the web server both via HTTP as well as via HTTPS. If you’d want to only allow HTTPS requests from and to your web server, you’d have to first enable the most restrictive rule, which in this case would be Nginx HTTPS, and then disable the currently active Nginx Full rule:
sudo ufw allow "Nginx HTTPS" sudo ufw delete allow "Nginx Full"
Allow SSH
When working with remote servers, you’ll want to make sure that the SSH port is open to connections so that you are able to log in to your server remotely.
The following command will enable the OpenSSH UFW application profile and allow all connections to the default SSH port on the server:
sudo ufw allow OpenSSH
Although less user-friendly, an alternative syntax is to specify the exact port number of the SSH service, which is typically set to 22 by default:
sudo ufw allow 22
Allow Incoming SSH from Specific IP Address or Subnet
To allow incoming connections from a specific IP address or subnet, you’ll include a from directive to define the source of the connection. This will require that you also specify the destination address with a to parameter. To lock this rule to SSH only, you’ll limit the proto (protocol) to tcp and then use the port parameter and set it to 22, SSH’s default port.
The following command will allow only SSH connections coming from the IP address 203.0.113.103:
sudo ufw allow from 203.0.113.103 proto tcp to any port 22
You can also use a subnet address as from parameter to allow incoming SSH connections from an entire network:
sudo ufw allow from 203.0.113.0/24 proto tcp to any port 22
Allow Nginx HTTP / HTTPS
Upon installation, the Nginx web server sets up a few different UFW profiles within the server. Once you have Nginx installed and enabled as a service, run the following command to identify which profiles are available:
sudo ufw app list | grep Nginx
Output Nginx Full Nginx HTTP Nginx HTTPS
To enable both HTTP and HTTPS traffic, choose Nginx Full. Otherwise, choose either Nginx HTTP to allow only HTTP or Nginx HTTPS to allow only HTTPS.
The following command will allow both HTTP and HTTPS traffic on the server (ports 80 and 443):
sudo ufw allow "Nginx Full"
Allow All Incoming HTTP and HTTPS
If you want to allow both HTTP and HTTPS traffic, you can create a single rule that allows both ports. This usage requires that you also define the protocol with the proto parameter, which in this case should be set to tcp.
To allow all incoming HTTP and HTTPS (ports 80 and 443) connections, run:
sudo ufw allow proto tcp from any to any port 80,443
Allow MySQL Connection from Specific IP Address or Subnet
MySQL listens for client connections on port 3306. If your MySQL database server is being used by a client on a remote server, you’ll need to create a UFW rule to allow that access.
To allow incoming MySQL connections from a specific IP address or subnet, use the from parameter to specify the source IP address and the port parameter to set the destination port 3306.
The following command will allow the IP address 203.0.113.103 to connect to the server’s MySQL port:
sudo ufw allow from 203.0.113.103 to any port 3306
To allow the entire 203.0.113.0/24 subnet to be able to connect to your MySQL server, run:
sudo ufw allow from 203.0.113.0/24 to any port 3306
Exercise
- Add a rule to access the web server of Ubuntu VM.(port 80)
- Add a rule to access the VNC server of Ubuntu VM.(port 5900)
- Drop all traffic form 192.168.1.0/24 (your local Network) and allow only SSH from your Host PC.
Gufw
Gufw is a Graphical firewall powered by UFW (Uncomplicated Firewall).
https://help.ubuntu.com/community/Gufw
Linux Desktops
In this Lab we will look in to how to install different Desktop Environments for Ubuntu 22.04.
Install Cinnamon GUI on Ubuntu 22.04
If you are on the latest 22.04 LTS, you don’t need to add any third-party repository, just use the below command:
sudo apt install cinnamon
then reboot the system.
Switch to Cinnamon from Gnome
After installing this traditional Linux desktop environment, close the command terminal, and log out of the system. Now, click on the user name, and before typing your password, click on the Gear icon given on the right bottom side. A pop-up will appear, select the Cinnamon, and then enter your password.
Uninstall or Remove Cinnamon
So, in case you didn’t like this Desktop Environment and don’t want a dual Graphical user interface setup then again switch back to the Ubuntu Default interface as we did in the above step.After that open the command terminal and run the following commands:
sudo apt autoremove --purge cinnamon
Install Budgie Desktop on Ubuntu 22.04
Unlike some other Linux distros, we don’t need to add any third party repository to get the packages to install Budgie, it is already available to fetch through the base repository of Ubuntu.
sudo apt install ubuntu-budgie-desktop
While installing the budgie desktop, the system will ask you to select the default display manager. Select the LightDm which is default display manager for Budgie desktop in Solus. Then reboot the system.
Switch to Budgie from Gnome
After installing this traditional Linux desktop environment, close the command terminal, and log out of the system. Now, click on the user name, and before typing your password, click on the Gear icon given on the right bottom side. A pop-up will appear, select the Budgie, and then enter your password.
Uninstall or Remove Budgie Desktop
sudo apt autoremove --purge ubuntu-budgie-desktop
Attachments (6)
- image1.png (14.1 KB ) - added by 4 years ago.
- image2.png (44.0 KB ) - added by 4 years ago.
- image3.png (45.5 KB ) - added by 4 years ago.
- image4.png (43.7 KB ) - added by 4 years ago.
- image5.png (49.1 KB ) - added by 4 years ago.
- image6.png (4.1 KB ) - added by 4 years ago.
Download all attachments as: .zip